What is the Datavant Site Connect Agent?
When we connect to on-premise EHR / PM systems, Datavant Site Connect requires the installation of the Datavant Site Connect agent. The agent allows Datavant Site Connect to safely and securely connect, extract, and transfer data to the Datavant Site Connect data lake.
Security
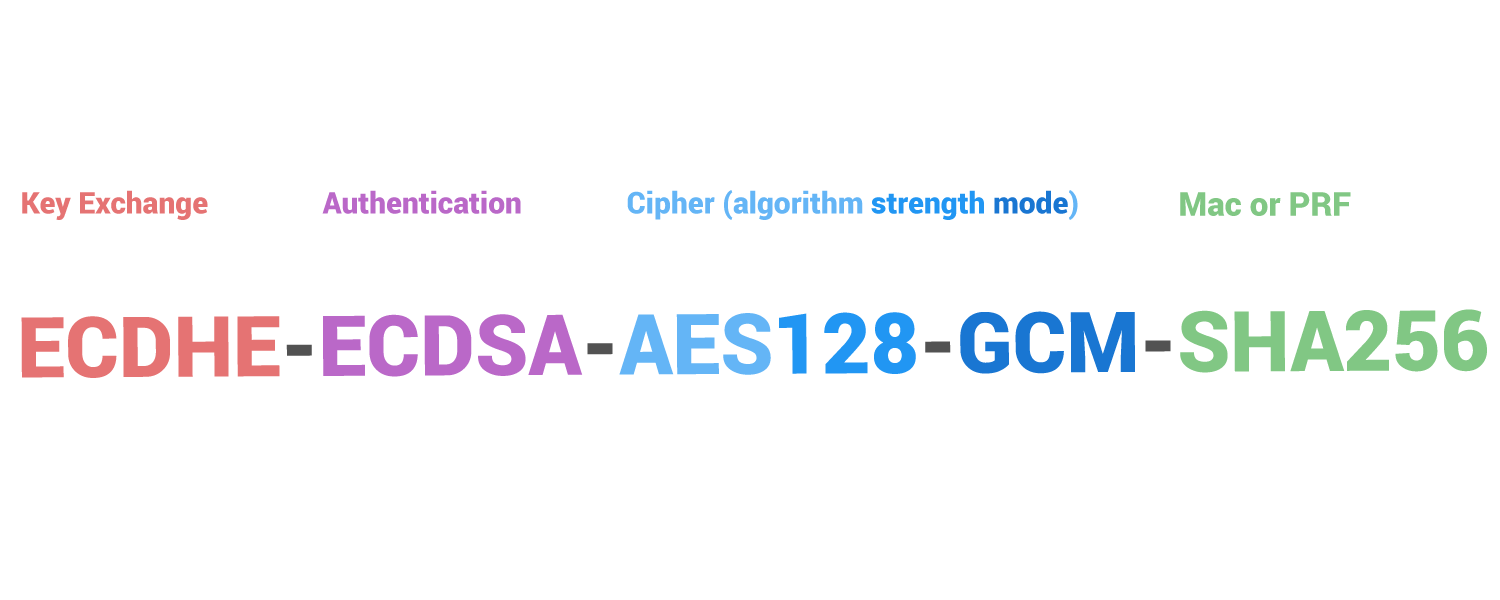
We won’t be delving too deeply into the finer details of the TLS handshake as it’s a very complicated, technical process. In the most simple terms, it’s a series of messages exchanged between the Datavant Site Connect agent and Datavant Site Connect wherein the server’s public key and SSL certificate are authenticated, culminating in creating a session key, which is what encrypts the connection between the client and the server. Combined, the total array of security protocols utilized between Datavant Site Connect and the agent host is the Cipher suites.
Cipher suites dictate how the entire process plays out. The agent running on the EHR server or application server sends the Datavant Site Connect server a list of the cipher suites it supports, and the server will choose a mutually supported cipher suite that it deems most secure. Depending on the version of TLS being used, this may happen before the handshake or in the very first step.
Example Cipher Suite:
To understand how our security protocols play out during Datavant Site Connect agent activity, let's walk through what the Datavant Site Connect agent is doing when it's time to transmit data back to the Datavant Site Connect server.
1. Polling
At the installation time, you or your Datavant Site Connect Installation engineer would have requested and set a nightly extraction time. This time the agent will begin to pull the data each day. The Datavant Site Connect Agent will wait for this time each day before extracting data from the source EMR/PM. It does this by polling via API calls to the Datavant Site Connect Cloud servers and waiting for a response that tells the agent the time has come to run the extraction logic.
Security Fact
-
Key Exchange: When polling the Datavant Site Connect server, the agent initiates the handshake by sending a "hello" message to the server. The message will include which TLS version the client supports, the cipher suites supported, and a string of random bytes known as the "client random." In reply to the client hello message, the server sends a message containing the server's SSL certificate, the server's chosen cipher suite, and the "server random," another random string of bytes generated by the server. The SSL certificates are valid for 13 months, and are renewed 60 days before expiration.
Note: Datavant Site Connect utilizes AWS load balancers that support a wide range of Cipher Suites to ensure connection compatibility. That being said, we also refuse connections to outdated or insecure cipher suites that could put the data at risk. For this reason, Datavant Site Connect advocates against installing the agent on personal laptops and workstations which do not undergo the same regular security and os updates that a standard EHR or Application server would.
2. Extraction
Once the agent and Datavant Site Connect have agreed upon a secured and mutually supported cipher suite, the Datavant Site Connect servers will respond to the agent API polling at the designated time by sending prebuilt SQL scripts specifically written to extract the Datavant Site Connect data model from the source EHR database. Once the extraction jobs are received by the EHR database server, the scripts are executed by the server hosting the agent. The results of the executed scripts are temporarily stored in the application directory.
Security Fact
-
Authentication: When the connection handshake is agreed upon, the Datavant Site Connect Server will send the agent its SSL certificate. The agent checks to make sure the certificate is "authentic". This is an extremely important step. To truly have a secure connection, you can’t just encrypt your data, you also need to know it’s being sent to the right website/organization. SSL/TLS certificates provide that authentication.
3. Transfer
Once a data file has been extracted from the source database, the file is sent via the encrypted connection to the Datavant Site Connect data lake for processing.
Security Fact
-
Cipher: Datavant Site Connect Servers leverage various Bulk Data Encryption algorithms to ensure Data being transferred between the client and server securely. AES_128_GCM represents it in the example above. To see the full range of supported suites, click here.
At Rest
Datavant Site Connect utilizes Amazon Simple Cloud Storage (S3). Data contained within the Datavant Site Connect S3 deployment are encrypted via AES256 utilizing Amazon S3-Managed Keys (SSE-S3). Once all of the data has been received for the evening, the agent returns to a "long-polling" state and awaits commands to extract data again.
Security Fact
- MAC: The Hashing Algorithms are fixed-sized blocks representing data of arbitrary size. They are used to verify the integrity of the data being transmitted. When the message is created, a hash of the original message is generated using the agreed-upon algorithm (i.e., MD5, SHA, SHA256, SHA384, SHA512). The receiver uses that hash to ensure that the data is the same as when the sender sent it.
Datavant Site Connect is dedicated to the security of the data we have been entrusted to manage, from transmission to storage. We regularly update our load balancers and servers to ensure we are supporting the latest available cipher suites and utilize the latest encryption algorithms supported by AWS S3.
Furthermore, maintenance of our existing supported cipher suites is an important function of certificate lifecycle management to ensure that our certificates are up-to-date with industry best practices.